5.2. Decentralization Reality Check
5.2.1. What this section covers (and what it doesn’t)
This section evaluates how decentralized Terra Classic is in practice, across three “control planes”:
Consensus control (stake distribution): who can coordinate influence over block production and network direction
Governance control (decision capture): who participates in votes, and how much voting power sits with validators who routinely do not vote
Operational control points: non-stake centralization risks (e.g., “who controls critical surfaces” such as core repositories and canonical routing)
Out of scope here: validator economics (5.3), governance mechanics/outcomes and execution rate (5.4), and organizational accountability design (5.5).
5.2.2. Decentralization snapshot (headline indicators)
Table 5.2-A — Decentralization headline indicators (consensus layer)
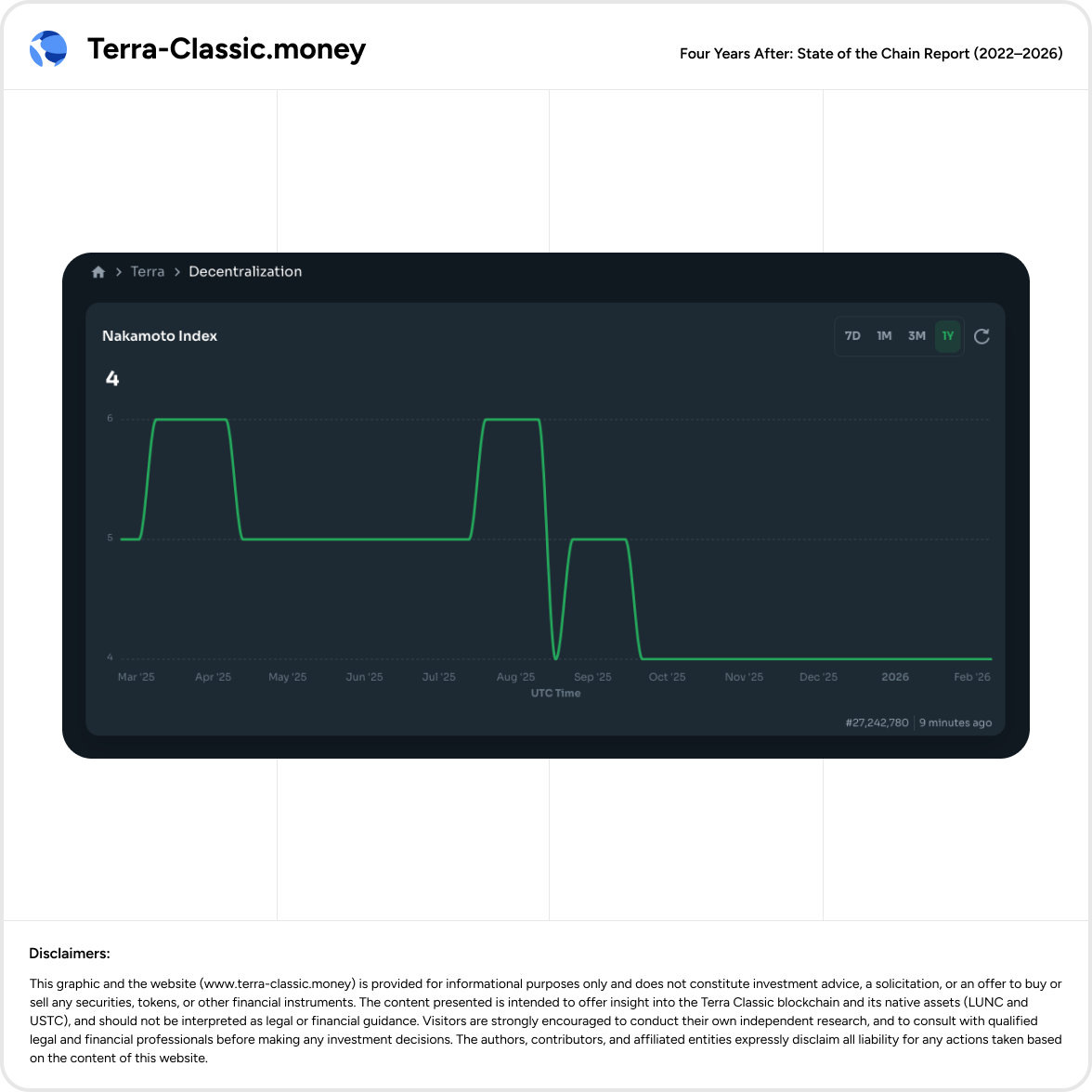
Interpretation: A Nakamoto Index of 4 implies that decentralization at the consensus layer is highly concentrated. Even without debating exact thresholds, the index communicates a simple operational reality: a small number of entities can be decisive in system-critical scenarios.
5.2.3. Validator “Sybil-like” clustering and undeclared operator groups (governance capture risk)
What this section means by “Sybil-like” in PoS.
In Proof-of-Stake governance, “Sybil attack” usually means one entity operating multiple validators (multiple identities) to accumulate disproportionate influence over consensus and voting—especially when delegators interpret validators as independent operators. In practice, this often looks like validator clustering: multiple validators controlled by the same people, team, or tightly coupled business entity.
Why this matters in Terra Classic (state today).
Terra Classic governance and decentralization metrics already show high concentration (e.g., Nakamoto Index ≈ 4). In that context, validator clustering is not a theoretical concern—it amplifies real-world capture risk, because the system’s “many validators” surface can mask fewer independent decision-makers.
Important evidence constraint (transparency statement).
Unlike stake distribution, clustering is not always provable purely on-chain. This report treats clustering as a governance-risk signal when one or more of the following is true:
the operator self-discloses control/ownership links publicly;
the affiliation is openly discussed in community channels by involved parties;
the validators share branding, public operator identity, or clearly linked entities/projects.
This is a risk analysis, not an accusation of criminal intent.
Community-identified clusters (examples with material governance relevance)
The following examples are widely discussed in the community as non-independent operator clusters (i.e., the practical “Sybil-like” pattern), and are treated here because they influence perceived decentralization and governance integrity:
A) LUNCLIVE-associated cluster (3 validators under one operator group)
LUNCLIVE🎙🔥
LUNA CLASSIC DAO
Alpine Digital
Community context: described as a linked group (two members + a partner connected via an L2 relationship), effectively operating multiple validator identities.
B) TerraCVita / Rexyz-associated cluster (2 validators; plus potential ecosystem influence)
TerraCVita 🌎 Minimum Fee + Auto Compounding
Terraport
Community context: frequently described as controlled by the same core actor(s) behind TerraCVita/Terraport; also discussed as having major influence in TerraCasino (influence level not treated as confirmed control unless verified).
C) JESUSisLORD cluster (explicit multi-validator operation)
JESUSisLORD
JESUSisLORD 2
Community context: openly justified by the operator as operating a second validator; illustrates the “nothing stops this” dynamic.
D) Juris Protocol / LuncGoblins overlap (governance perception risk)
Juris Protocol | $JURIS…
LuncGoblins (100% $BLAME buyback)
Community context: key individuals are described as overlapping (co-founder/lead contributor). Even when operators are trusted and competent, overlapping control still reduces effective decentralization.
E) Additional small clusters (low individual significance, but cumulative signal)
Community examples include “Blue Team / Red Team”-style paired validators (illustrative of “multiple identities” behavior). Individually small; collectively they reinforce the pattern that multi-validator operation is tolerated.
Why this is being ignored is part of the decentralization problem
The deeper issue is not that clustering exists—permissionless PoS will always allow it. The deeper issue is that Terra Classic has no credible social or governance counterweight:
No strong norm of operator disclosure (“one operator, multiple validators” must be declared).
No systematic labeling in major dashboards/explorers (“operator group” tags).
No incentives discouraging multi-validator concentration when Nakamoto Index is already low.
Investor and ecosystem impact
Decentralization optics diverge from reality.
Even if the chain shows 100+ validators, clustering can mean far fewer independent decision-makers.Governance capture risk increases.
If one operator controls multiple validators, they can amplify turnout, shape quorum dynamics, and coordinate votes more effectively than the “independent operator” assumption implies.Delegator decision-making is misled by default.
Delegators selecting “different validators” may unknowingly pick multiple validators within the same operator group.
Minimum remediation standard (pragmatic, not ideological)
This report does not propose banning multi-validator operation outright. It proposes transparency and risk controls:
Mandatory disclosure norm: if you operate more than one validator, disclose the operator group on your validator page and public channels.
Dashboard labeling: explorers/dashboards should tag validators by operator group where publicly known.
Delegator guidance: publish a “unique operator set” list so delegators can choose truly independent operators.
Governance guardrails (optional): explore policy constraints or incentive mechanisms that reduce operator-group dominance in voting power (details in Chapter 11 risk/diagnosis).
Bottom line.
In a network already showing high concentration, validator clustering is a meaningful governance-risk multiplier. Treating it as “normal” without disclosure and labeling makes reported decentralization materially overstated relative to real decision independence.
5.2.4. Governance decentralization is not just “who can vote,” but “who does vote”
On-chain governance only behaves as a decentralized decision system if participation is broad enough to prevent decision capture by a small active minority, and if “inactive” validators do not hold enough latent power to swing outcomes opportunistically.
This report uses validator non-participation as a direct decentralization signal because:
non-voters still hold voting power, and
non-participation shifts effective control to the subset that consistently votes.
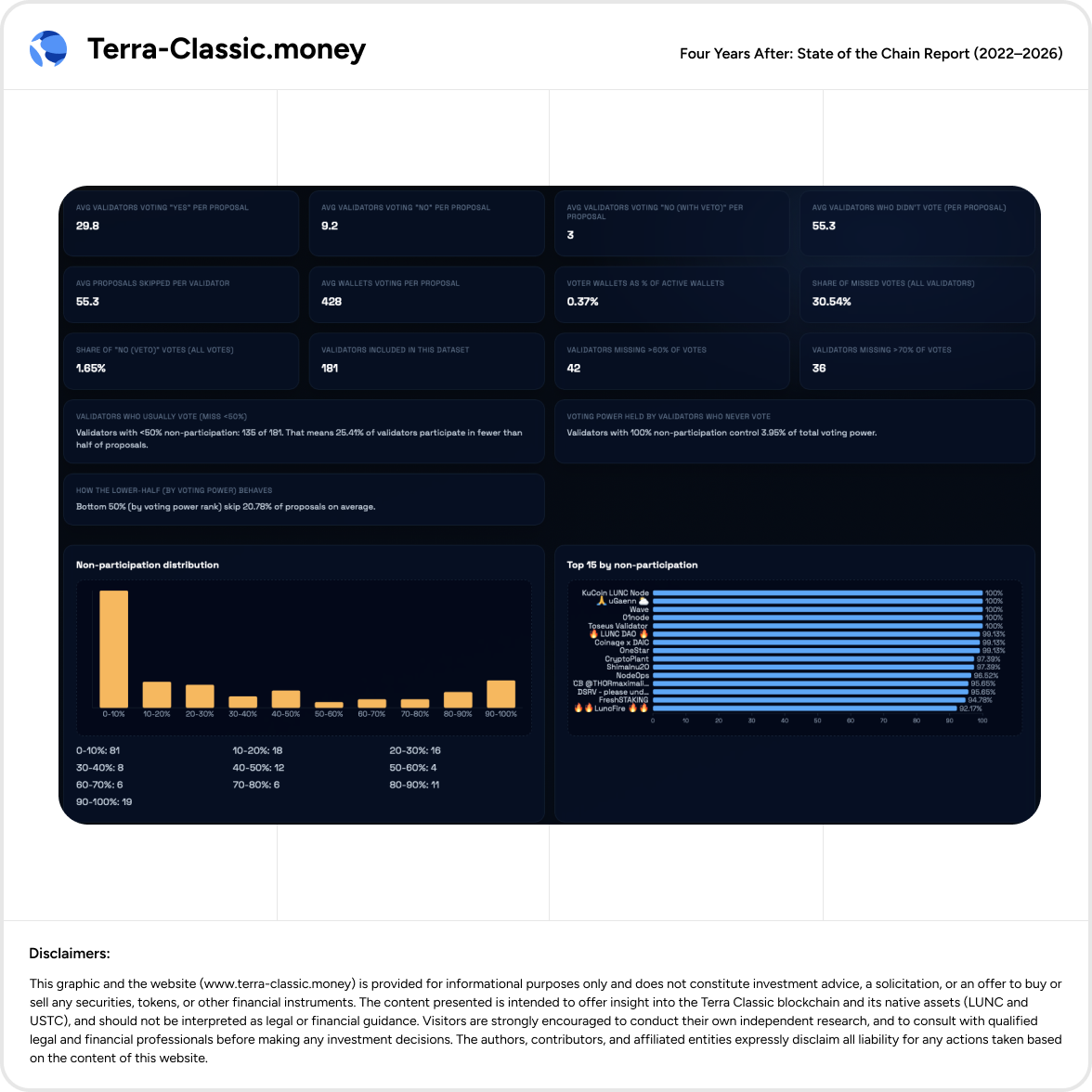
Table 5.2-B — Governance participation distribution (Last 1 year)
Interpretation (1Y): The validator set is not behaving like a broadly engaged governance body. A substantial share of votes are simply not cast, and “never voters” control double-digit voting power in the last-year window.
5.2.5. Two-year baseline: structurally weak, even when “better than last year”
It is possible for governance decentralization to fluctuate year to year. The relevant question is whether the system is structurally healthy.
Table 5.2-C — Governance participation distribution (Last 2 years)
Interpretation (2Y):
Even in the longer baseline, governance non-participation remains high enough to be a systemic problem (≈30% of validator votes not cast).
The 1Y window suggests a worsening in practice: “never-voter voting power” rose from 3.08% (2Y) to 13.38% (1Y).
This is a decentralization problem because it reduces governance legitimacy and makes outcomes more sensitive to a small set of active actors.
5.2.6. Decision capture rules (how this report interprets the data)
This report makes its decentralization assessment explicit and reproducible by applying simple interpretation rules to the above metrics.
Table 5.2-D — “Decision capture” interpretation rules
Interpretation: Terra Classic triggers the “bad” zone on multiple metrics at once: low NI (4), high 1Y never-voter voting power (13.38%), and a high share of votes not cast (30–40% across windows).
5.2.7. Operational decentralization: control points beyond stake
Delegated stake is only one decentralization surface. On a live L1, effective control often concentrates in “control planes” that sit above stake: code merge rights, release engineering, canonical information routing (official links that exchanges and aggregators display), and critical infrastructure & interfaces that users treat as “the chain.” When these control planes are thinly staffed or concentrated, the network can be stake-decentralized on paper while being operationally centralized in practice.
This section documents the operational control points that matter most for Terra Classic and why they create “single point of failure / capture” risk—even without overt malicious intent.
5.2.7.1. Core codebase control: who can approve/merge changes (GitHub bus factor)
A credible operational decentralization assessment starts with the simplest question: how many independent individuals can approve and merge code for the chain and its core operational repos?
A structured scan of PR histories across repositories in the classic-terra GitHub organization found evidence that at least nine individuals possess write/maintainer privileges (approval and/or merge) across the organization, with StrathCole and kien6034 appearing as the most active maintainers in recent periods.
The same scan identifies the maintainer set (based on observed merges/approvals across 2023–2026 activity) as including, at minimum:
StrathCole
kien6034
fragwuerdig
nghuyenthevinh2000
TropicalDog17
hoank101
inon-man
LuncBurner
ZaradarBH (historical merge rights evidenced earlier in the project)
This is not “one person controls everything,” and that matters—but it is still a thin set for a production L1 aspiring to compete with leading Cosmos networks. The risk profile is not only malicious capture; it is also availability risk:
If 1–2 primary maintainers reduce activity, the chain’s ability to ship upgrades and respond to incidents degrades sharply.
Review capacity becomes a bottleneck: even with open PR submission, throughput depends on a small reviewer/merger pool.
Why this is investor-relevant: thin merge capacity increases upgrade latency, patch latency, and institutional fragility (success depends on continuity of a few key operators). It also increases the likelihood that governance becomes performative: proposals can pass, but delivery depends on a limited maintainer surface.
5.2.7.2. “Governance-approved dev list” vs real operational reality (process centralization)
Separate from raw GitHub activity, Terra Classic has repeatedly debated rules for who can merge code—including frameworks involving “KYCed” or governance-approved maintainers.
In validator/developer discussions, an explicit rule set is described where:
anyone may contribute code via PRs,
anyone may review/comment,
but merging and releases are restricted to a governance-approved list (modifiable via governance).
This introduces a structural tension:
It can improve accountability and reduce “unknown contributor” risk.
But it also formalizes centralization around a small approved set, which can become a gatekeeping surface.
A separate developer chat excerpt illustrates how narrow this can become in practice, referencing a scenario where “currently only” a very small set could approve PRs and where enforced rules required multiple approvals from people with write access.
Bottom line: even when stake is widely distributed, the chain’s evolution is constrained by a small operational group—both socially (who is trusted) and technically (who has merge/release rights).
5.2.7.3. Canonical information routing: “official” links as a control plane (terra-classic.io / third-party profiles)
A highly underappreciated centralization surface is canonical link routing—the website and “official resources” that appear on CoinMarketCap / exchange listings / token profiles. Whoever controls that destination influences:
where new users go,
what tools are perceived as official,
and which validators / communities / dApps receive visibility.
In validator/developer discussions about third-party information relayers and custodianship, the process is explicitly framed as governance-driven, with documentation intended to live under classic-terra/documents and changes managed through PR workflows and an approved “dynamic list management” team.
Separately, the Agora discussion referenced (and covered) frames domain custody as “ultimate control over the destination” and flags the systemic risk of concentrating multiple “control planes” (core code + canonical link target + major tooling) under one operator—even assuming good faith.
Why this is decentralization-critical: governance can vote on intent, but domain ownership + deployment authoritydetermines what actually ships and what users see. This is an operational capture surface: “control of where the world points” becomes control of narrative + onboarding + default choices.
5.2.7.4. Infrastructure & interface concentration: stacked roles and single-point-of-failure risk
Operational centralization risk is amplified when the same individuals hold influence across multiple critical surfaces simultaneously (code + infra + interface + canonical routing).
The Agora excerpt provided describes this explicitly as “centralization of power at ecosystem-critical level / single point of failure risk,” listing a pattern of stacked roles and warning that—even absent wrongdoing—this concentration contradicts the decentralization narrative and increases systemic risk.
This matters because users don’t interact with “the chain” abstractly—they interact through:
interfaces (front-ends),
endpoints (RPC/LCD/FCD relayers),
explorers/dashboards,
and “official” links.
If these surfaces become concentrated, the network becomes operationally fragile:
outages have wider blast radius,
governance disputes spill into “what users see,”
and recovery depends on a small number of operators.
5.2.7.5. What “good” looks like (practical decentralization targets)
Terra Classic does not need perfection; it needs credible reduction of single points of failure. A reasonable decentralization target state for an L1 includes:
Codebase bus factor: increase the number of active reviewers/mergers; document roles; ensure redundancy (no single maintainer dominates merges for long periods).
Release process transparency: published release checklists, reproducible builds, clear sign-off policy, and public incident retrospectives.
Canonical link governance: domain custody and deployment processes that cannot be unilaterally changed; multi-sig / multi-admin controls; clear content policy.
Interface / infra plurality: multiple independent endpoints and interfaces widely used; avoid a “one front-end to rule them all” reality.
Investor framing: today, Terra Classic can be described as stake-decentralized enough to run, but operationally centralized enough to be fragile—especially relative to the decentralization story it often markets.
5.2.8. Key takeaways for investors (box)
Decentralization is currently a material structural risk for Terra Classic.
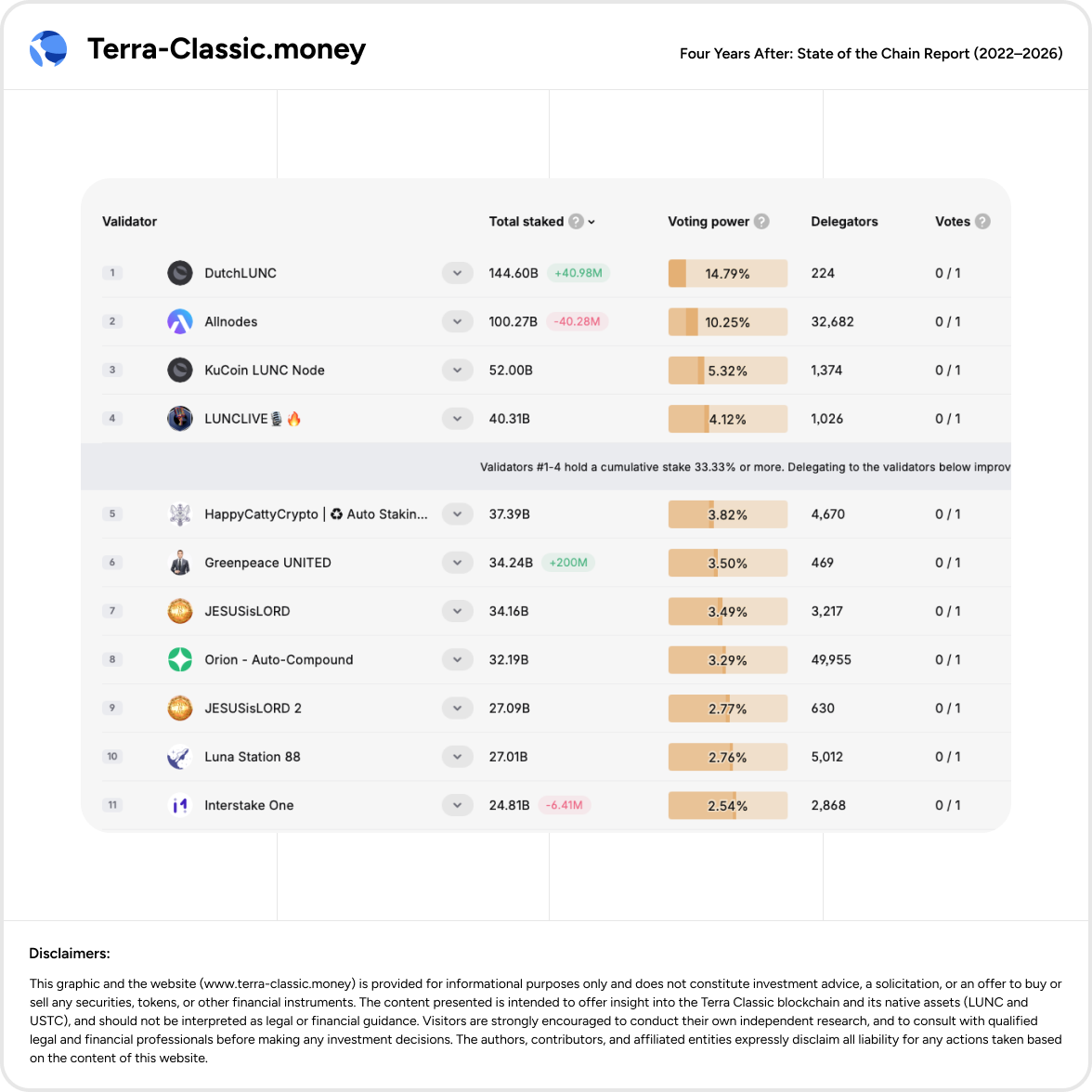
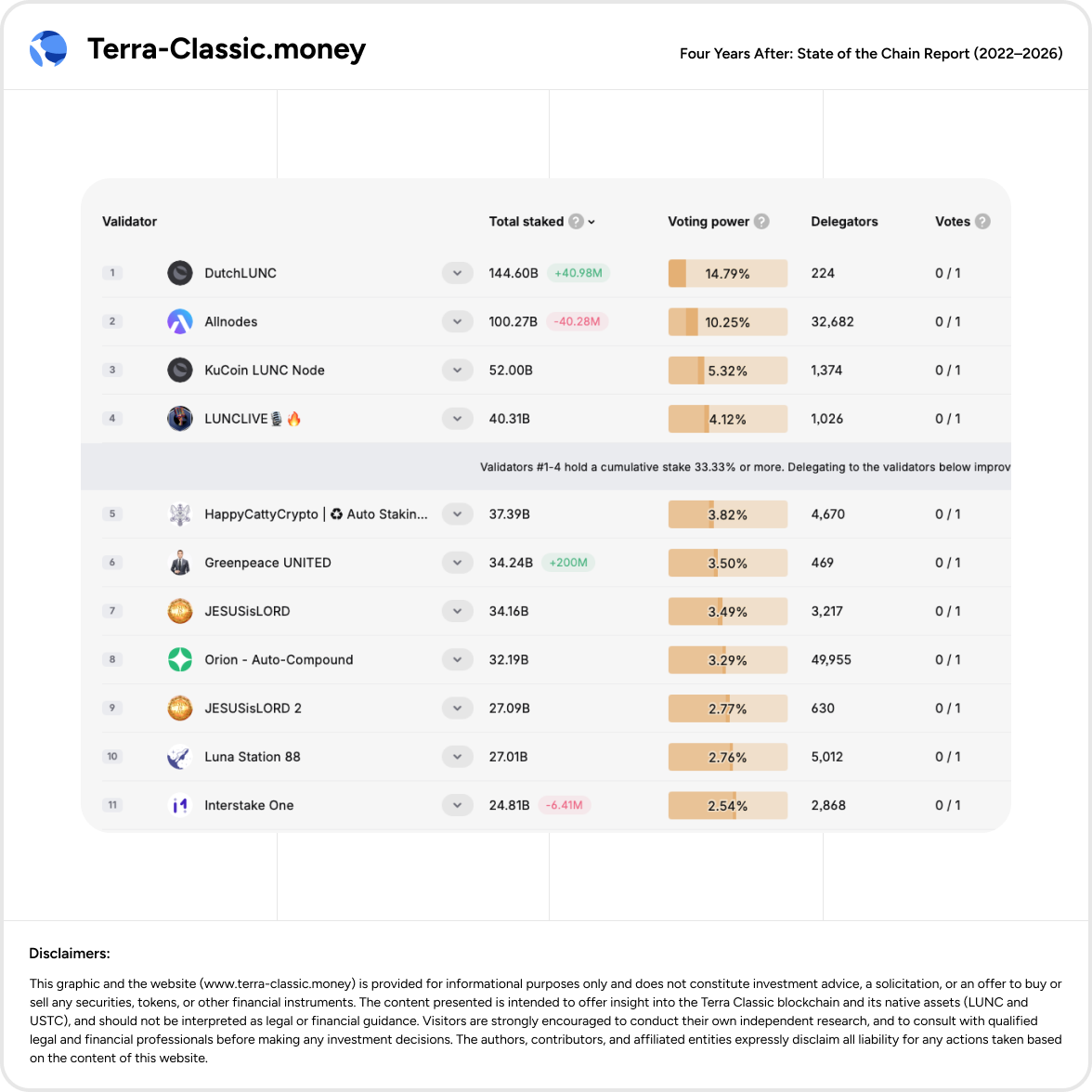
Consensus concentration is high: Nakamoto Index 4 and top-4 stake ≥ 33.33%.
Governance participation is weak: 30–40% of validator votes are not cast; in the last-year window, “never voters” control 13.38% voting power.
Operational decentralization is weaker than stake decentralization: core code merges, release authority, and canonical information routing (official links/interfaces) concentrate control beyond what stake metrics alone imply.
Validator clustering (“Sybil-like” multi-validator operators) further reduces effective decentralization.Multiple validators are widely understood to be operated by the same groups (examples listed in 5.2.X), meaning the number of independent decision-makers can be materially lower than the headline validator count.
Why this matters: Higher concentration increases the probability of governance capture, slower upgrades, partner reluctance, and a credibility discount in markets that reward robustness and redundancy.